Module 2 – IT Security
Lesson 1 – Security Concepts and Data Threats
IT security is about protecting computers, networks, data and online services from harm or unauthorised access.
This lesson follows the ICDL Cyber Security syllabus section on Security Concepts and introduces
the key ideas behind information security, the value of information, and the main types of threats that people and
organisations face.
Learning outcomes
By the end of this lesson, you should be able to:
- Explain the difference between data and information, and why information is valuable.
- Describe cybercrime, hacking and risks related to cloud services.
- Outline the CIA triad: confidentiality, integrity and availability.
- Recognise the roles of users, policies and management in security.
- Distinguish between threats, vulnerabilities and risks.
- Identify different types of data threats, including social engineering and data interception.
- Describe common social engineering methods and identity theft techniques.
- Explain basic file security, physical security and backup controls.
- Recognise the possible consequences of poor security.
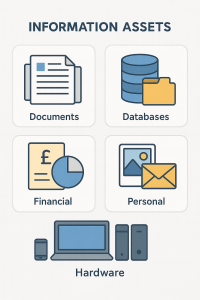
1. Information and assets
1.1 Data and information
In IT security, it is important to understand the difference between data and information:
- Data – raw facts or figures without context (for example, numbers, dates, codes).
- Information – data that has been processed or organised so it has meaning and value.
Cybercriminals target information because it can be used for identity theft, fraud and other crimes.
In IT security, information refers to any data that has value to a person or organisation.
Examples of valuable assets:
- Customer records and contact details.
- Financial data such as invoices, accounts, salaries.
- Personal files such as photos, documents and messages.
- Business plans, designs, research and intellectual property.
- Login credentials and passwords.
- IT hardware and devices.
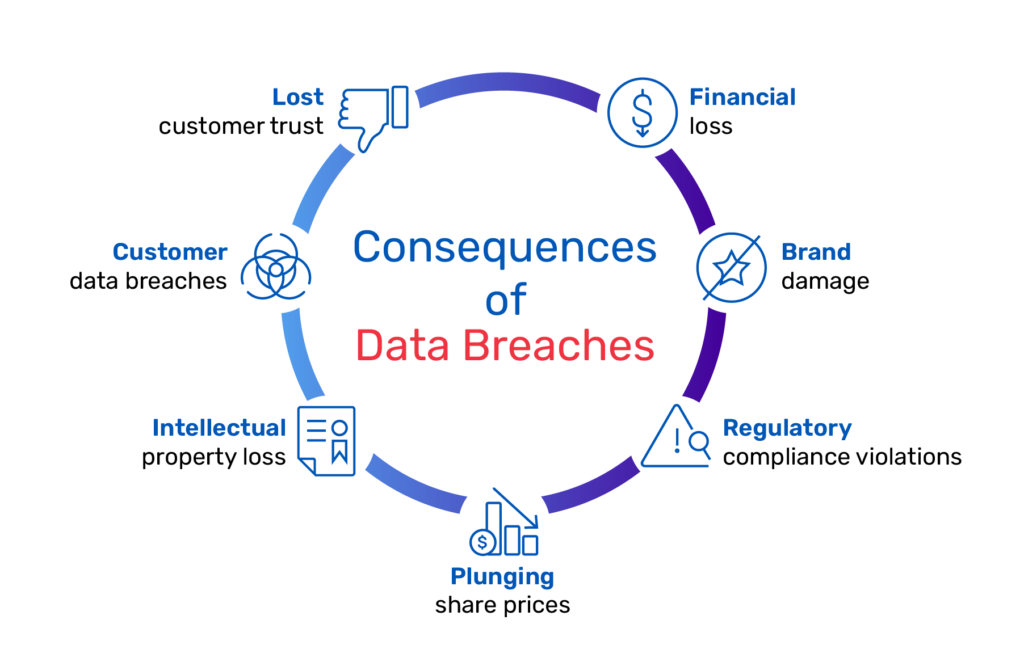
If this information is lost, stolen or damaged, consequences may include:
- Financial loss.
- Loss of reputation and customer trust.
- Legal penalties and fines.
- Disruption of services or operations.
Quick check: Data or information?
- “27, 34, 19” – this is data (just numbers).
- “Average age of customers is 27” – this is information (data with meaning).
1.2 Cybercrime, hacking and cloud risks
- Cybercrime – criminal activities that use computers, networks or the internet (for example, online fraud, data theft, ransomware attacks).
- Hacking – attempting to gain unauthorised access to systems, accounts or data.
Threats can come from:
- Individuals – employees, ex-employees, customers, criminals.
- Service providers – cloud or hosting companies mishandling or losing data.
- External organisations – competitors, criminal groups, hostile groups.
Using cloud computing (storing data on remote servers) is convenient but introduces risks such as:
- Less direct control over where data is stored.
- Potential loss of privacy if data is accessed or processed improperly.
- Dependency on the provider’s security measures and policies.
Think about it
Make a quick list of three types of information that are most valuable to you personally
(for example, photos, bank details, email account).
What might happen if each of these were stolen?
2. The CIA triad – core security goals
IT security is often described using the CIA triad:
- Confidentiality – only authorised people can access the information.
- Integrity – information should remain accurate and unaltered unless authorised.
- Availability – information and systems must be accessible when needed.
Examples:
- Confidentiality – protecting medical records from unauthorised access.
- Integrity – preventing unauthorised changes to financial records.
- Availability – ensuring online banking and critical systems work reliably.
2.1 Value of personal and workplace information
- Protecting personal information helps avoid identity theft, fraud and loss of privacy.
- Protecting workplace information helps prevent theft, fraudulent use, accidental loss and sabotage.
2.2 Data/privacy principles and roles
Common data/privacy protection principles include:
- Transparency – people know how their data is collected and used.
- Legitimate purposes – data is collected for clear, lawful reasons.
- Proportionality – only the amount of data necessary is collected and kept.
Key terms:
- Data subject – the person the data relates to.
- Data controller – the organisation that decides how and why personal data is processed.
It is important to follow organisational guidelines and policies for ICT use, as well as legal requirements such as GDPR.

Quick check: CIA triad
Match each situation to the CIA goal it affects most:
- Server crash makes the website unavailable → Availability
- Someone changes marks on a student record → Integrity
- A stranger accesses private medical files → Confidentiality
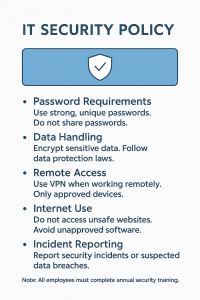
3. Users, policies and responsibilities
Security requires people, policies and technology working together.
- Security policy – rules for safe system use (passwords, email, internet, mobile devices).
- End user – must use systems responsibly, follow procedures and report issues.
- IT/security staff – manage firewalls, antivirus, backups, monitoring and incident response.
- Management – must support security with training, resources and clear policies.
Additional syllabus items:
- Access control – ensures only authorised users can access systems/data.
- Least privilege – users have only the access they need to do their job.
- Data protection compliance – following laws such as GDPR and organisational policies.
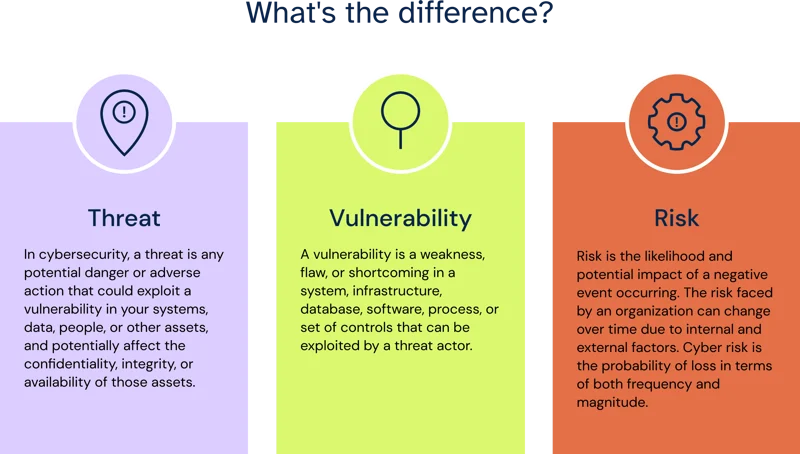
4. Threats, vulnerabilities and risks
Key security terms:
- Threat – something that can cause harm (hacker, malware, fire, flood).
- Vulnerability – a weakness that could be exploited (weak passwords, unpatched software).
- Risk – the chance that a threat will exploit a vulnerability and cause damage.
Example:
- Threat: cybercriminal sending phishing emails.
- Vulnerability: staff not trained to spot phishing.
- Risk: someone clicks the link and gives away their password.
Threats can be:
- Malicious – deliberate actions by attackers or dishonest insiders.
- Accidental – mistakes by users or service providers.
- Environmental/extraordinary – fire, floods, war, earthquake, power failure.
Self-check: Spot the vulnerability
Which of these is a vulnerability?
- A storm causes a power cut – this is a threat.
- Using the same weak password on every site – this is a vulnerability ✅
- Laptop stolen from a car – this is the impact/result of a risk.
5. Types of data threats
Data can be harmed in many ways:
- Accidental loss – deleting a file by mistake.
- Accidental damage – dropping a device, liquid spills.
- Deliberate attacks – hacking, data theft, malware.
- Environmental threats – fire, flood, theft, natural disasters.
- Technical failures – disk failure, server crash, power issues.
Additional required threat types:
- Social engineering – manipulating people (phishing, vishing phone calls, impersonation, shoulder surfing).
- Malware – viruses, worms, Trojans, ransomware (covered in the next lesson).
- Data interception – data stolen during transmission over insecure networks.

6. Personal security – human factors
People are often the weakest point in security.
6.1 Social engineering
Social engineering is the manipulation of people to gain unauthorised access or information. It can lead to fraud and data breaches.
Common methods:
- Phone calls – pretending to be support staff, banks or officials.
- Phishing – fraudulent emails, texts or websites.
- Shoulder surfing – watching someone enter a PIN or password.
6.2 Identity theft
Identity theft occurs when criminals use someone’s personal details without permission for personal, financial, business or legal gain.
Methods include:
- Information diving – searching bins or old documents for personal data.
- Skimming – copying card details using a skimming device.
- Pretexting – creating a false story or role to trick someone into giving information.
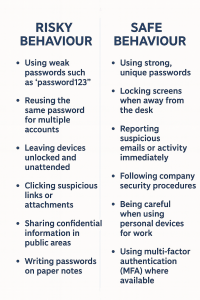
6.3 Risky and good behaviour
Common risky behaviour:
- Using weak passwords.
- Reusing passwords across different sites.
- Leaving devices unlocked.
- Clicking suspicious links or opening unexpected attachments.
- Sharing confidential information publicly.
- Posting sensitive content online.
- Writing passwords on sticky notes.
Good security behaviour:
- Using strong, unique passwords.
- Locking screens when leaving a desk.
- Reporting suspicious activity.
- Following company procedures and policies.
- Being careful with personal devices at work.
- Using multi-factor authentication (MFA) where possible.
Scenario: Social engineering
You receive a call from someone claiming to be “IT support”, asking for your password so they can
“fix your email quickly”.
- Never share your password over phone or email.
- End the call and contact your official IT helpdesk using known contact details.
- Report the incident as a suspected social engineering attempt.
7. File security basics
File security helps protect data stored on devices from misuse or unauthorised access.
7.1 Macro security
- Documents and spreadsheets can contain macros (small programmes that automate tasks).
- Malicious macros can run harmful code when the file is opened.
- Enabling higher macro security settings reduces the risk of malicious macros running automatically.
7.2 Encryption and passwords
- Encryption scrambles data so it can only be read with the correct password, key or certificate.
- It protects sensitive files, folders or drives if a device is lost or stolen.
- It is important not to disclose or lose the encryption password, key or certificate.
- Files such as documents, spreadsheets and compressed (zipped) files can be protected with passwords.
Quick check: File security
Which of these offers better protection if your laptop is stolen?
- Just using a Windows login password.
- Full disk encryption plus a strong login password ✅
8. Physical security
Physical security protects devices and data from unauthorised physical access or theft.
- Locking rooms, server cabinets and offices.
- Using access cards, codes or biometrics.
- Security cameras (CCTV).
- Using laptop security cables.
- Never leaving devices unattended in vehicles.
- Shredding sensitive documents.
- Keeping backups in secure locations.

9. Consequences of poor security
If IT security is weak, consequences may include:
- Data breaches – sensitive data exposed.
- Financial loss – fraud, fines, lost business.
- Reputation damage – loss of customer trust.
- Operational disruption – systems offline, services unavailable.
- Legal issues – breaking data protection laws or contracts.
10. Basic security controls and backups
Simple security measures can reduce risk significantly.
- Use strong passwords.
- Enable multi-factor authentication (MFA).
- Lock your device when away.
- Install operating system and app updates.
- Use reputable antivirus software.
- Use secure Wi-Fi networks.
- Encrypt sensitive files.
- Back up important data regularly.
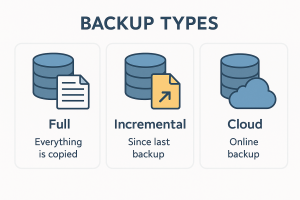
Backup types:
- Full backup – everything is copied.
- Incremental backup – only recent changes.
- Cloud backup – automatic online backups.
Self-check: Improving security
Which three actions would most improve security on a home laptop?
- Installing updates regularly ✅
- Using a strong unique password ✅
- Backing up important files ✅
- Writing passwords on a sticky note ❌
11. Practical activity
- List five types of information that are valuable to you personally.
- List five types of information valuable to an organisation.
- Identify three threats that could affect your home computer or phone.
- Identify three vulnerabilities in your behaviour (for example, weak passwords, no backups).
- Write three changes you can make today to improve your IT security.
