Module – Cyber Security
Lesson 2 – Malware and Protection
This lesson follows the ICDL Cyber Security syllabus section on malware.
It explains what malware is, the main types of malware, how it is concealed and spreads,
and the practical steps used to protect against and remove it.
Learning outcomes
By the end of this lesson, you should be able to:
- Define malware and explain how it can affect different types of devices.
- Describe common ways malware is concealed and spread.
- Recognise main malware categories (viruses, worms, ransomware, spyware, etc.).
- Identify typical signs that a device may be infected.
- Explain how antivirus, updates and safe behaviour help prevent malware.
- Outline sensible steps to take if malware infection is suspected.
1. What is malware?
Malware (malicious software) is any programme or code created to damage a device,
disrupt systems, steal information, or gain unauthorised access. It can affect desktop computers,
laptops, smartphones, tablets and other connected devices.
Malware often runs silently in the background. Users may not realise their device is infected
until performance changes or data is lost.
Common ways malware is concealed or spreads:
- Trojans, rootkits and backdoors that hide inside apparently legitimate software or deep in the operating system.
- Email attachments containing malicious code (for example, a fake invoice with a dangerous macro).
- Links in emails, text messages or social media posts that lead to infected or fake websites.
- Drive-by downloads from compromised or malicious websites that install malware automatically.
- Infected USB drives and other removable media connected to a device.
- Pirated or cracked software, films or music downloaded from untrusted sources.
- Mobile apps from unofficial app stores or unknown publishers.
- Exploiting vulnerabilities in outdated operating systems, browsers or applications.

Quick check: Is this a malware risk?
- Opening a Word document with macros from an unknown sender → High risk ✅
- Updating your browser from its official website → Low risk
- Plugging in a found USB stick from the street → High risk ✅
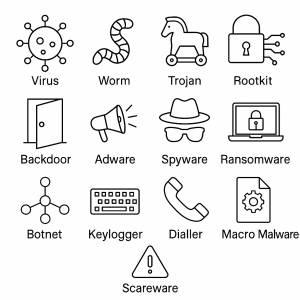
2. Types of malware
The ICDL syllabus requires candidates to recognise main malware categories and how they operate.
Many real attacks combine several types, such as a Trojan that installs ransomware and spyware together.
2.1 Infectious malware – viruses and worms
Viruses
- Attach themselves to legitimate files or programmes.
- Spread when infected files are opened, shared or copied to other systems.
- Can corrupt, delete or modify files, or slow down the system.
Traditional viruses usually require user action, such as opening an infected attachment.
Worms
- Spread automatically across networks without user action.
- Exploit network or operating system security weaknesses.
- Can generate heavy network traffic and cause systems to crash.
Worms are particularly dangerous in organisations because they can move quickly between many connected devices.
2.2 Data theft, profit and extortion malware
Adware
- Displays unwanted adverts, pop-ups or banners.
- May redirect the web browser to advertising or malicious websites.
- Sometimes comes bundled with “free” software.
Ransomware
- Encrypts files or even the whole system, so that data cannot be accessed.
- Shows a ransom message demanding payment to unlock data.
- Targets individuals and organisations such as businesses, hospitals and councils.
Important: Paying the ransom is not recommended. There is no guarantee the data will be restored and it encourages further criminal activity.
Spyware
- Secretly monitors user activity on the device.
- Can capture usernames, passwords, banking details and browsing history.
- Often sends collected information to an attacker over the internet.
Botnets
- A botnet is a group of infected devices remotely controlled by an attacker.
- Used for sending spam, launching large-scale attacks or mining cryptocurrency.
Keystroke logging
- Keyloggers record keyboard input (keystrokes).
- Used to steal passwords, PINs and other sensitive information.
Diallers
- Malicious programmes that control how a device connects to networks or services.
- Can connect to premium-rate numbers or services without the user’s knowledge, generating high charges.
2.3 Other hiding techniques
Rootkits and backdoors
- Rootkits hide deep inside the operating system to avoid detection.
- Backdoors provide secret remote access to a device or system.
Macro malware
- Hidden inside documents (for example Word or Excel files) that contain macros.
- Runs when macros are enabled by the user.
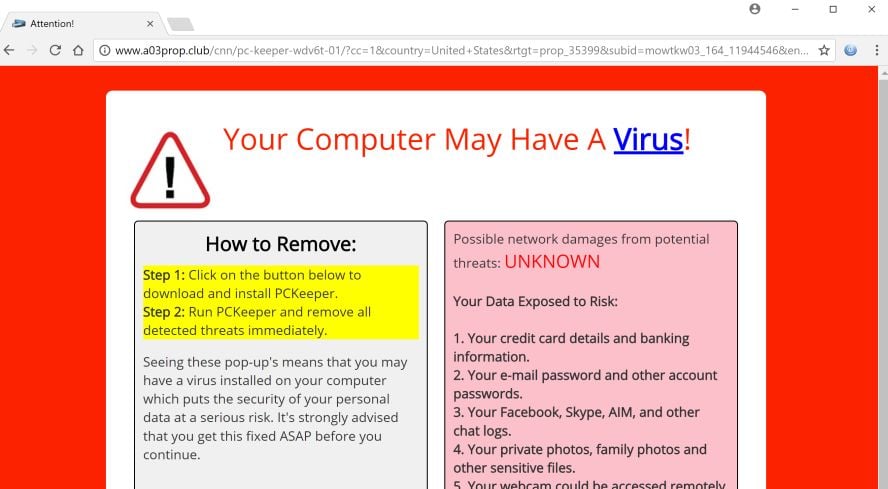
Scareware
- Displays fake alerts claiming that the device is infected or unsafe.
- Tricks users into installing further malware or paying for unnecessary “clean-up” software.
Self-check: Match the malware type
- Encrypts your files and asks for money → Ransomware
- Shows lots of unwanted adverts → Adware
- Secretly records everything you type → Keylogger (spyware)
- Turns your PC into part of a remote “army” → Botnet
3. Signs of malware infection
Candidates should be able to recognise typical symptoms that may indicate malware on a device.
These symptoms do not always prove infection but should trigger further checks.
- System runs unusually slowly or freezes frequently.
- Applications crash or fail to open as expected.
- New programmes or browser toolbars appear that you did not install.
- Unexpected pop-ups, adverts or warning messages.
- Web browser is redirected to unfamiliar websites.
- Home page or search engine changes without your permission.
- Security software (antivirus, firewall) is disabled or cannot be updated.
- Files become encrypted, missing, or renamed without explanation.
- Unusual network activity, especially when the device is idle.
- Contacts report strange emails or messages sent from your account.
Scenario: Is your device infected?
Yesterday your browser homepage changed, you now see constant pop-ups, and your antivirus
keeps turning itself off. These are strong signs of a possible malware infection.
Next step: Disconnect from the internet and run a full antivirus scan.
4. Protecting against malware
Effective protection uses both technical controls and safe behaviour.
No single measure is enough; several measures should be used together.
4.1 Antivirus and anti-malware software
- Scans files, programmes and downloads for known threats using signature databases and behaviour-based detection.
- Should be installed on computers and devices.
- Must be updated regularly so that new malware can be detected.
- Full system scans should be run regularly (for example, weekly) and when infection is suspected.
4.2 Software updates and obsolete software
- Operating systems, browsers, plug-ins and applications must be kept up to date.
- Security updates (patches) fix known vulnerabilities that malware can exploit.
- Automatic updates should be enabled where possible.
- Using obsolete or unsupported software increases malware risk and may cause incompatibility problems.
4.3 Safe usage practices
- Be cautious with email attachments and links, especially if unexpected.
- Avoid pirated or cracked software and untrusted download sites.
- Only install apps from official stores or trusted publishers.
- Scan removable media (USB drives, memory cards) with antivirus before opening files.

Quick check: Best protection
Which combination is most effective?
- Antivirus only.
- Antivirus + regular updates + careful behaviour ✅
- Just “being careful” with no updates or antivirus.
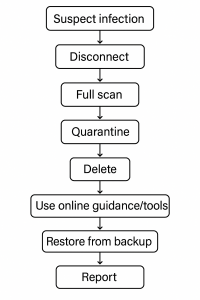
5. Resolving and removing malware
When malware is suspected or detected, follow a structured process.
In a workplace, always follow local policies and involve IT support where required.
- Disconnect from the internet or network to reduce the risk of further spread or data theft.
- Run a full antivirus/anti-malware scan using up-to-date software.
- Quarantine infected or suspicious files so they cannot run but are kept isolated for review.
- Delete infected/suspicious files once you are sure they are not needed.
- If your usual tools cannot resolve the problem, use trusted online resources
such as the websites of operating system, antivirus or web browser providers, or relevant
national cyber-security authorities, for guidance and specialised tools. - Restore clean copies of files from a trusted backup if data has been damaged or encrypted.
- After the device has been cleaned, change passwords for important accounts.
- In organisations: report incidents immediately according to company policy.
Scenario: You think your PC has malware
- Disconnect from Wi-Fi or unplug the network cable.
- Run a full scan with your security software.
- Follow the recommendations (quarantine or remove files).
- Restart if advised, then scan again.
- Restore any lost files from a clean backup.
- Change passwords for key accounts (email, banking, work systems).
6. Practical activity
- Check that antivirus or endpoint protection is installed and active on your device.
- Run a manual full system scan and review the results.
- Check update settings for your operating system and main applications. Confirm that automatic updates are enabled.
- List three realistic ways malware could spread in your home, school or workplace, and write down how each can be prevented.
- Create a short personal checklist of safe downloading and email practices that you will follow.
